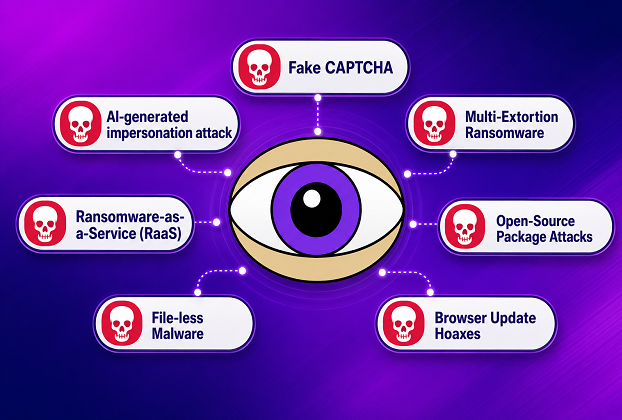
For decades, cybersecurity revolved around a pretty darn simple idea: malicious files infect computers, antivirus software detects and fixes them, and users stay protected. That traditional model is now dangerously out of whack. Modern cybercriminals no longer rely solely on exploiting software vulnerabilities. Instead, they increasingly target the most unpredictable and emotionally driven component in the digital ecosystem — human beings.
This shift has opened a can of worms for individuals and organizations alike. Today’s attackers understand psychology almost as well as they understand code. They know how to create urgency, fear, trust, curiosity, and confusion in the blink of an eye. In many cases, the user unknowingly delivers the coup de grâce to their own system by clicking, pasting, approving, or authorizing something malicious.
The fallout from these attacks can be, and many a times is devastating. Financial theft, ransomware infections, identity compromise, business disruption, and even reputational collapse are becoming alarmingly common. A plethora of new cyber attack tactics have emerged for a couple of years, and many of them no longer depend on traditional malware delivery methods per se. Instead, they underpin a new generation of “human-operated compromise”.
This article explores some of the latest and lethal malware scams targeting humans and explains how attackers manipulate behavior rather than merely attacking machines through penetration tactics.
1. Fake CAPTCHA Malware (ClickFix) Attack
Attack Type
Human-assisted malware execution through fake verification prompts.
Tactic:
One of the most alarming trends in recent years is the fake captcha malware attack. Victims visit a compromised or malicious website and are shown a convincing “I’m not a robot” verification page. However, instead of performing a normal CAPTCHA check, the page silently copies a malicious command into the user’s OS clipboard and instructs them to press Win+R, Ctrl+V, and Enter.
This windows run command virus scam abuses legitimate Windows tools like ‘rundll32.exe’ or PowerShell to execute remote payloads. The process looks harmless enough that many users obediently follow it without realizing they are effectively granting attackers direct access to their systems.
Why is it dangerous
This attack is particularly dangerous because it bypasses traditional security assumptions. Antivirus products often monitor suspicious downloads, but here the victim voluntarily launches the malicious process themselves. The psychological manipulation is the real tactic here.
The attack flow is frighteningly effective:
User sees a fake security check. They assumes the request is legitimate and then executes the command.
The Malware installs in the blink of an eye.
Many victims never even realize what happened until the fallout begins.
Prominently Appeared Since
2025
Some prominent Cyber Threats names
ClickFix campaigns, Lumma Stealer, DarkGate, NetSupport RAT.
Precautions and Fixes
A real CAPTCHA never asks users to open the Windows Run dialog or paste commands into the system. Users should immediately leave any site requesting such actions. Keeping browser security features enabled and getting ahead of the curve through cybersecurity awareness training is now as important as antivirus software itself.
2. AI-Powered Deepfake Social Engineering
Attack Type
AI-generated impersonation attacks.
Tactic:
Artificial intelligence has given attackers global reach unlike anything seen before. Criminals now generate fake voice calls, realistic video impersonations, and highly personalized phishing emails. In some incidents, employees received calls that sounded exactly like company executives authorizing urgent financial transfers.
Attackers no longer need a shred of knowledge about programming to launch devastating campaigns. AI tools now automate much of the deception process.
Why is it dangerous
Humans are biologically wired to trust familiar voices and faces. Deepfake attacks exploit this instinct masterfully. The de facto security rule of “verify the sender†becomes difficult when the sender looks and sounds authentic.
A striking fictional demonstration of AI-powered deepfake social engineering appeared in the film Mission Impossible — Dead Reckoning Part One, where the Entity manipulated communications by mimicking trusted voices. In one scene, the AI deceives Benji Dunn — Ethan Hunt’s IMF teammate and technical operations expert — by faking voice instructions and steering him toward the wrong course of action. The sequence illustrates a lethal reality of modern cyber threats: when attackers can convincingly imitate someone you already trust, even experienced professionals can unknowingly drop the ball. What once looked like science fiction is now rapidly becoming a real-world cybersecurity challenge.
This is a hard pill to swallow for many organizations because traditional awareness training is no longer sufficient. Even trained professionals can drop the ball when confronted with emotionally convincing AI-generated requests.
Prominently Appeared Since
2025
Some prominent Cyber Threats names
Deepfake CEO scams, AI-enhanced phishing kits, synthetic identity fraud networks.
Precautions and Fixes
Organizations should require secondary verification for sensitive requests, especially financial approvals. Voice alone should never underpin trust decisions. Multi-factor verification processes remain critical.
3. Multi-Extortion Ransomware
Attack Type
Advanced ransomware blackmail operations.
Tactic:
Ransomware groups have evolved dramatically. Previously, attackers encrypted files and demanded payment. Today, they steal confidential data first, threaten public leaks, contact customers directly, and sometimes launch DDoS attacks simultaneously.
This layered extortion model throws a wrench into traditional disaster recovery planning. Even companies with good backups can still face catastrophic exposure.
Why is it dangerous
The attack is designed to corner victims psychologically and operationally. The objective is no longer merely technical disruption; it is public humiliation and maximum pressure.
Businesses may discover that their sensitive contracts, employee records, or customer information are as good as dead once criminals threaten publication.
Prominently Appeared Since
2025
Some prominent Cyber Threats names
LockBit, BlackCat/ALPHV, Cl0p, Akira.
Precautions and Fixes
Organizations should maintain offline backups, implement zero-trust principles, and continuously monitor for suspicious lateral movement. Incident response plans should include public relations and legal preparation, not just technical recovery.
4. Ransomware-as-a-Service (RaaS)
Attack Type
Cybercrime franchising.
Tactic:
Cybercrime has become industrialized. Skilled developers now create ransomware platforms and rent them to affiliates for profit sharing. In effect, ransomware has become software-as-a-service for criminals.
This business model allows inexperienced attackers to wreak havoc using sophisticated tools with no strings attached beyond revenue sharing agreements.
Why is it dangerous
The barrier to entry for cybercrime has collapsed. A teenager with minimal technical expertise can now launch attacks on par with professional hacking groups from just a few years ago.
This democratization of cybercrime has dramatically increased the volume of attacks worldwide.
Prominently Appeared Since
2025
Some prominent Cyber Threats names
LockBit affiliates, Black Basta, Royal ransomware groups.
Precautions and Fixes
Organizations must adopt layered defense strategies. Endpoint monitoring, employee training, access segmentation, and privileged account management are no longer optional luxuries.
5. Supply Chain and Open-Source Package Attacks
Attack Type
Compromise through trusted software dependencies.
Tactic:
Modern applications depend on thousands of external packages and libraries. Attackers exploit this trust relationship by compromising open-source repositories or injecting malicious code into legitimate software updates.
Developers may unknowingly install infected packages while trying to speed up projects or avoid spinning their wheels on repetitive coding tasks.
Why is it dangerous
Supply chain attacks cast a shadow over the entire software ecosystem because they exploit trust itself. A single compromised package can infect thousands of organizations midstream before anyone detects the intrusion.
The infamous SolarWinds incident helped expose how devastating these attacks can become.
Prominently Appeared Since
2025
Some prominent Cyber Threats names
3CX compromise, malicious npm packages, PyPI malware campaigns.
Precautions and Fixes
Organizations should verify package integrity, restrict unnecessary dependencies, and continuously audit third-party software components. Blind trust in external libraries is becoming the final nail in the coffin for many security strategies.
6. Fileless Malware and Credential Abuse
Attack Type
Invisible attacks using legitimate system tools.
Tactic:
Instead of installing traditional malware files, attackers abuse existing Windows utilities such as PowerShell, WMI, or Remote Desktop Protocol. These attacks often rely on stolen usernames and passwords rather than malicious executables.
This makes detection extraordinarily difficult because the attacker appears to be using normal administrative behavior.
Why is it dangerous
Traditional antivirus systems look for malicious files. Fileless attacks leave very little behind. In many cases, security teams do not realize attackers are present until the criminals deliver the final blow.
Attackers can quietly move through networks, collect credentials, and exfiltrate data for weeks or months.
Prominently Appeared Since
2025
Some prominent Cyber Threats names
Cobalt Strike abuse, Emotet follow-on attacks, PowerShell-based intrusion frameworks.
Precautions and Fixes
Strong password policies, multi-factor authentication, restricted administrative privileges, and behavior-based detection systems are essential. Monitoring user behavior anomalies is now more important than merely scanning files.
7. Fake Cloudflare Verification Pages and Browser Update Hoaxes
Attack Type
Fake browser security and update scams.
Tactic:
Another rapidly growing scam involves fake Cloudflare verification pages or bogus browser update prompts. Victims believe they are updating Chrome, Edge, or another trusted application, but the download actually installs spyware or remote access trojans.
This tactic exploits familiarity and urgency. Attackers play devil’s advocate by pretending to help users remain “secure.â€
Why is it dangerous
Many users trust recognizable brands blindly. Criminals understand this psychological shortcut extremely well. That is exactly how fake cloudflare captcha spreads malware so effectively.
The scam works because the page appears polished, professional, and believable. Users fiddle with browser permissions or execute downloads voluntarily, unaware of the nefarious payload hidden underneath.
Prominently Appeared Since
2025
Some prominent Cyber Threats names
SocGholish, FakeBat, DarkGate delivery campaigns.
Precautions and Fixes
Software updates should only come from official vendor websites or built-in browser update mechanisms. Random pop-up update prompts should never be trusted.
Humans Are the New Attack Surface
The biggest cybersecurity lesson of the modern era is unsettling but unavoidable: attackers increasingly target human psychology instead of merely targeting machines.
This transformation changes everything.
Modern malware campaigns no longer depend entirely on exploiting operating system vulnerabilities. Instead, they exploit impatience, curiosity, panic, authority, convenience, and trust. That shift is what makes these new cyber attack tactics so effective.
The old cybersecurity mindset focused heavily on technical defense system:
* Firewalls * Antivirus software * Intrusion prevention systems
Those tools still matter. But today’s threat landscape demands something more: human awareness and vigilance.
A user who understands how manipulation works can stop an attack before it even begins to invade. Conversely, one moment of panic or distraction can open the gates to catastrophe in the blink of an eye.
The reality is stark: modern cybercrime is no longer just a technical problem. It is a psychological battlefield.
And understanding that may be the single most important defense of all.