Blockchain technology has emerged as one of the most disruptive innovations of the modern era. It challenges traditional models of trust, transparency, and decentralization, offering new ways for industries and individuals to interact, transact, and store data. In this flagship article, we take an insightful journey through blockchain’s fundamentals, its core components, practical applications, and deeper technical aspects. Structured in a comprehensive Question & Answer format, this article preserves detailed explanations, examples, code snippets, and structured data to provide both clarity and depth for enthusiasts, developers, and decision-makers alike.
Blockchain technology is a method of digitally recording information in a way that makes it extremely difficult to change, hack, or manipulate. It’s a decentralized, distributed digital ledger that stores transactional records, known as blocks, across a network of computers. This distributed nature makes it secure and transparent, as each transaction is verified by multiple participants and cannot be altered without consensus from the network.
Primary Building Blocks / Components of a Blockchain Technology
Here are the primary building blocks or components of a Blockchain Technology.
Decentralized
Blockchain doesn’t rely on a central authority like a bank. Instead, it spreads data across many independent computers a.k.a nodes. This structure reduces the risk of system failure or control by a single party, making the network more secure and democratic.
Distributed Ledger
Each participant in the blockchain network holds a complete, synchronized copy of the ledger. This ensures transparency, as all users see the same transaction history, eliminating the need for third-party verification.
Immutable
Once a transaction is confirmed and recorded on the blockchain, it cannot be changed or deleted. This immutability is enforced through cryptographic hashing and the block structure, ensuring data integrity and trustworthiness.
Blocks and Chains
Transactions are bundled into blocks, which are linked in sequence to form a chain. Each block contains a unique hash of the previous one, making the entire chain strictly resistant to tampering and alteration.
Consensus Mechanisms
Before a transaction is added, the network must agree it’s validity through a process called consensus. Mechanisms like Proof of Work or Proof of Stake ensure that all participants trust the accuracy of the data without a central governing authority or overseer.
Tokenization
Tokenization is the process of converting physical or digital assets into digital tokens on a blockchain. These tokens can represent anything from real estate and art to stocks or in-game items. It enables fractional ownership, easy transfer, and increased liquidity of assets in a secure and transparent manner.
Where do the Blocks in a Blockchain get stored, and in whose custody? and how are they identified individually? Is it Blockchain address or a link or some hash value?
Where Are Blocks Stored in a Blockchain?
Storage Location
Blocks are stored on the local storage of each full node in the blockchain network. A node is any computer or device that participates in maintaining the blockchain ledger by downloading and verifying data.
Every full Node stores the entire blockchain ledger (i.e., a copy of every block ever created). This includes all transactions, metadata, hashes, and timestamps.
Custody
Blockchain is a decentralized custody. No single person or organization holds custody. Every full node independently holds its own copy. Therefore, the blockchain is public and redundant — even if some nodes go offline, the data survives on others and never become inaccessible.
How Are Blocks Identified?
Each block is uniquely identified by a cryptographic hash. The hash is a SHA-256 hash (in Bitcoin and many other blockchains) and it is derived from the block’s contents:
Timestamp
List of transactions
Nonce
Previous block’s hash
Merkle root (summary of all transactions)
Example:
Block Hash: 00000000000000000003c3fe74c6f54d06b23336a49cb19f9b9e4c7ff4db8dd1
This hash is like the digital fingerprint of the block — any change to its data changes the hash, breaking the chain.
How Are Blocks Linked?
Each block contains the hash of the previous block, forming a linked list structure:
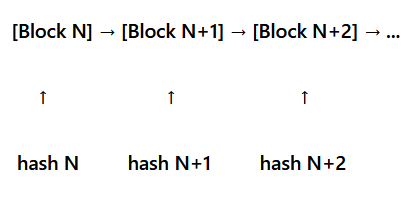
This is what ensures immutability: if someone tries to change one block, they’d have to recompute all following hashes, which is computationally infeasible on a public blockchain like Bitcoin or Ethereum.
Is the Block Identified by a Blockchain Address?
No. A block is not identified by a blockchain address. A blockchain address refers to a user’s wallet address (e.g., where coins are sent/received). A block is identified by its unique hash, not an address.
Summary Table
| Concept | Description |
| Where stored? | On every full node’s local disk (globally distributed) |
| Who holds custody? | No one — everyone (decentralized) |
| Block Identifier? | SHA-256 hash of block’s data (not an address or link) |
| Linked by? | Each block stores previous block’s hash — creating a chain |
| Can blocks change | No — any tampering changes the hash and breaks the chain |
Analogy
It’s akin to a massive, shared spreadsheet, where every row is linked to the previous one by a fingerprint. You can’t edit a past row without alerting the whole system — that’s the power of blockchain.
What is a Node in a Blockchain System?
A node is essentially a computing device (hardware) — usually a server, desktop, or even a virtual machine — that:
- Stores part or all of the blockchain (depending on node type)
- Verifies and validates blocks and transactions
- Relays data to other nodes in the network
- Executes blockchain protocol logic (consensus rules, smart contracts, etc.)
The nodes store every block, every transaction, and Metadata (like timestamps, hashes, addresses, etc.)
Lightweight nodes (also called SPV — Simplified Payment Verification nodes) don’t store all data. They just store headers.
The Nodes:
- Validate incoming transactions before they’re added to blocks
- Ensure no double spending, invalid signatures, and malformed transactions
- Depending on the blockchain, they may also run smart contracts (e.g., Ethereum)
Who is Supposed to Manage, Control, Add and Possibly Remove Individual Nodes. Is it a Sort of Master-node, a Person or What?
In public blockchains, nodes are self-managed and controlled only by protocol rules. In private or consortium blockchains, organizations or administrators decide who manages, adds, or removes nodes. There is no universal “master-node” that governs everything. If a node behaves the way it is not supposed to; like it doesn’t follow Proof-of-Work or Proof-of-Stake protocols, tries to broadcast invalid transactions or blocks, then other nodes simply ignore it. Hence, a corrupted node can exist, but it won’t influence the chain because its data won’t be accepted by honest nodes.
Further, on Public Blockchains any individual or the ones who represent the organization can run a node. on a Consortium Blockchain only the authorized entities like member organizations of the consortium or the vetted participants based on trust and compliance can run a node. On a Private Blockchain the ones who are explicitly invited or contracted, or the partners are authorized to run the node(s).
Note that the one who runs and manages a node must have an internet connection, and the required hardware and software to run the node. They’re responsible for keeping it synced, upgraded, and running 24/7.
What a Blockchain Token can Represent?
A token can represent any of the following:
- 1. Ownership of something
- Ownership of a digital or physical asset
Example: Real-estate tokenization, NFTs, shares in a project
- Ownership of a digital or physical asset
- 2. Authority or governance
- Voting power in a decentralized organization (DAO)
Example: UNI, COMP governance tokens
- Voting power in a decentralized organization (DAO)
- 3. Permission or access rights
- Access to services, platforms, features
Example: Filecoin (FIL) pays for storage; some tokens unlock premium app features
- Access to services, platforms, features
- 4. Currency-like value
- Many tokens behave like money on their platform
- Example: USDT , USDC, DAI (stablecoins)
- 5. Representation of external value
- Gold-backed tokens
- Dollar-backed tokens
- Stock-backed tokens
So in simple words block chain tokens can represent (but not limited to) payments, rewards, stable value, governance power, digital collectibles, and resource usage. The broader the recognition a blockchain system receives from the public and key institutions, the greater the value and influence of its token.
What are the Blockchain Platforms? Why are they required and what facilities do they provide?
What Are Blockchain Platforms?
A blockchain platform is a technology framework that allows developers and businesses to build, deploy, and manage blockchain-based applications or smart contracts. Think of it like an operating system, but dedicated for decentralized apps (dApps) and networks.
These platforms provide the tools, protocols, consensus mechanisms, and infrastructure to create and maintain a distributed ledger system without building everything from scratch.
Why Are Blockchain Platforms Required?
Blockchain platforms are needed because they abstract the complexities of building secure peer-to-peer networks and cryptographic validation from the ground up. They enforce trust and consensus without central authorities. They offer built-in support for smart contracts, token issuance, and permission management. They are programmable, allowing custom business logic (e.g., escrow rules, voting mechanisms, supply chain flows). Also they offer development kits, APIs, and testing tools that accelerate adoption.
Without a platform, implementing even a basic blockchain network would be nearly impossible on technical and economical grounds.
What Facilities Do Blockchain Platforms Provide?
| Feature | Description |
| Consensus Mechanisms | Protocols like Proof of Work (PoW), Proof of Stake (PoS), or PBFT to achieve agreement across nodes. |
| Smart Contract Engine | To deploy self-executing business logic (e.g., in Solidity, Rust, Go). |
| Network Management | Tools to configure public or private (permissioned) networks. |
| Ledger and State Management | Maintains transaction history and current state across nodes. |
| Token Management | Allows issuing, transferring, and tracking cryptocurrencies or digital assets. |
| Developer Tools | SDKs, APIs, IDE plugins, test networks (e.g., Ganache for Ethereum). |
| Security and Identity | Handles cryptographic identity, access control, and data integrity. |
| Governance Tools | DAOs, voting mechanisms, and update policies for network changes. |
| Interoperability | Some platforms support cross-chain transactions or bridges. |
| Analytics and Monitoring | Dashboards and logs to track network health and transaction performance. |
Examples of Popular Blockchain Platforms
| Platform | Focus | Language | Type |
| Ethereum | General-purpose dApps and smart contracts | Solidity | Public |
| Hyperledger Fabric | Enterprise-grade, permissioned | Go, Java | Private |
| Solana | High-performance DeFi and NFT apps | Rust, C | Public |
| Corda | Financial institutions, regulated environments | Kotlin, Java | Permissioned |
| Polkadot | Multi-chain interoperability | Rust | Public |
| Tezos | Formal verification and governance | Michelson | Public |
| Avalanche | Customizable blockchain subnets | Solidity | Public |
| Algorand | High-speed, low-fee smart contracts | TEAL, Python | Public |
How does a cryptocurrency like Bitcoin derive its value and become convertible to Fiat Currencies such as USD despite having no central authority backing it?
Why Bitcoin Has Value (Despite No Central Authority)
Scarcity
Bitcoin has a fixed supply: only 21 million coins will ever exist. This is hard-coded into its protocol. This scarcity mimics precious metals like gold — limited supply often leads to value if demand exists.
Demand and Utility
People believe Bitcoin has utility as a store of value, digital asset, and even a medium of exchange in some cases. As more people are willing to buy and hold Bitcoin, its demand grows, driving up the price.
Decentralization and Security
Bitcoin operates on a decentralized blockchain with thousands of computers (nodes) verifying transactions. In addition, the underlying technology is highly secure and transparent, creating trust without needing a central authority.
Trust and Consensus
The value comes from collective belief. If enough people trust Bitcoin and accept it as valuable, then it is valuable. Just like how fiat currency (e.g., USD) isn’t backed by gold anymore but is still accepted because people, organizations and countries trust the government behind it.
How Bitcoin is Converted to USD
You can convert Bitcoin to USD (or other currencies) using:
Crypto Exchanges
Platforms like Coinbase, Binance, Kraken, etc., allow users to buy and sell Bitcoin for USD or other fiat currencies. These platforms determine the exchange rate based on market supply and demand.
Peer-to-Peer Transactions
People can agree to exchange Bitcoin for cash or goods/services. The value is based on the current market rate, often tracked through online exchange listings.
Think of Bitcoin like digital gold. No government prints gold, no central bank sets its price, Yet people agree on its value and trade it globally.
Who are Crypto Miners and what’s their job? Are they like freelancers?
Crypto miners are individuals or companies that use powerful computers to solve complex mathematical problems, which helps validate transactions on a blockchain network. Their job is crucial because they keep the blockchain secure and running smoothly.
In a way, they can be like freelancers! Many miners work independently, setting up their own mining rigs and earning cryptocurrency rewards. Others join large mining pools, where multiple miners combine their computing power to increase their chances of solving a block and sharing the rewards. Some even work for big companies that run industrial-scale mining operations.
Unlike traditional freelancers, though, miners rely on expensive hardware, electricity, and technical expertise rather than client contracts. It’s more about competing with others to solve puzzles rather than offering a service to customers.
How does the Mining process work?
- Transaction Collection: When someone makes a cryptocurrency transaction, it gets bundled with other transactions into a “block.”
- Solving the Puzzle: Miners compete to solve a complex math problem using powerful computers. This problem involves finding a specific number that, when combined with the block’s data, creates a valid cryptographic hash (a unique digital fingerprint).
- Verification: The first miner to solve the puzzle shares their answer with the network. Other miners verify the solution to ensure it’s correct.
- Adding to the Blockchain: Once verified, the new block is added to the blockchain, a permanent public ledger of transactions.
- Reward Distribution: As a reward for their efforts, the successful miner earns newly minted cryptocurrency (such as Bitcoin) plus any transaction fees included in the block.
This process, known as Proof-of-work, ensures security, prevents fraud, and keeps the blockchain running as a decentralized yet reliable methodology.
What is the core purpose of Crypto Mining? Is it to develop the best suited Cryptographic Hash for the new block?
Yes, that’s an important part of it! But the core purpose of crypto mining goes beyond just finding the best cryptographic hash.
The primary goal is to validate and secure transactions on a decentralized network. Since cryptocurrencies like Bitcoin don’t rely on a central authority (like banks), miners play a crucial role in ensuring the integrity of transactions.
Here’s how mining serves its purpose:
- Transaction Verification: Miners confirm that transactions are legitimate, preventing double-spending or fraud.
- Block Creation: By solving the complex puzzle (finding the cryptographic hash), miners create new blocks and add them to the blockchain.
- Network Security: Mining helps maintain the decentralized nature of cryptocurrencies, making it extremely difficult for hackers to alter past transactions.
- New Coin Generation: Mining is also how new cryptocurrency enters circulation—miners earn rewards for their work, keeping the system running.
So yes, solving for the best cryptographic hash is the major part of the process, but the ultimate purpose is maintaining the blockchain’s security, integrity, and decentralization.
Please provide a comprehensive analogy that maps Blockchain system components to their counterparts in traditional Web and Mobile Application ecosystems.
Here’s a comprehensive analogy that maps blockchain system components to their counterparts in traditional web and mobile application ecosystems. This analogy is designed for technically aware readers who understand how web and mobile apps are hosted, served, secured, and accessed.
To understand blockchain at a technical level, let’s compare it to a traditional web or mobile application stack by mapping each familiar component to its blockchain counterpart.
Dedicated Web Server Machine Vs Blockchain Node (Full Node or Validator Node)
Just like a web server runs your website or app, a blockchain node runs a copy of the entire distributed ledger. Every node can independently validate transactions and maintain consensus, much like a dedicated server handles requests and serves content.
OS Installed on Web Server (Windows Server / Linux / Apache / Nginx) Vs Blockchain Protocol (Ethereum, Bitcoin, Hyperledger, Solana)
The OS is the substrate or the foundation layer on which other layers and apps are installed and configured. It provides the foundational rules and environment for apps to run. Similarly, the blockchain protocol defines how nodes interact, how blocks are formed, how consensus is achieved, and how smart contracts are executed.
Web Server Software (IIS / Apache / Nginx) Vs Blockchain Client Software (Geth for Ethereum, Bitcoin Core)
This software is installed on the node/server and implements the protocol (like HTTP/HTTPS handling in web servers). It handles communication between nodes, transaction validation, block propagation, and smart contract execution.
Encryption Technologies (SSL, TLS) Vs Cryptographic Functions (SHA-256, ECDSA, Public/Private Key)
SSL/TLS secure the communication between client and server. Blockchain uses hashing and public/private key cryptography to secure data, ensure integrity, and enable digital signatures for authentication and non-repudiation.
Databases (SQL Server, MySQL, MongoDB) Vs Blockchain Ledger (Distributed Ledger)
Traditional web, desktop and mobile apps store data in centralized databases. In blockchain system, data is stored de-centrally across all participating nodes in the ledger, a tamper-evident chain of blocks.
Backend Technologies (ASP.NET, Java, Node.js, PHP) Vs Smart Contract Platforms (Solidity for Ethereum, Chaincode for Hyperledger)
In traditional platforms Backend code handles business logic. In blockchain, smart contracts are the business logic — deployed to the blockchain and executed by nodes deterministically.
Server-Side Frameworks (Laravel, ASP.NET Core, Express.js) Vs Smart Contract Frameworks (Truffle, Hardhat, Remix, Brownie)
Server-side frameworks help organize, develop, and deploy backend logic in a seamless manner, whereas in Blockchain Smart contract frameworks provide tools to write, compile, test, and deploy contracts efficiently and seamlessly.
Client-Side Technologies (HTML, CSS, JavaScript, React, Angular, Flutter) Vs Web3 Frontends (DApps)
Just like web apps use frontend libraries for UI/UX, blockchain DApps use HTML/CSS/JS + Web3 libraries (e.g., Web3.js, Ethers.js) to interact with the blockchain. Frameworks like React + Web3.js build the frontend of DApps.
Client Interfaces (Browsers, Mobile Apps) Vs Web3 Browsers / Wallet Apps (MetaMask, Trust Wallet, WalletConnect)
Browsers and mobile apps access web content. Wallets act as gateways to the blockchain, allowing users to sign transactions, interact with DApps, and manage crypto assets securely.
API Gateways / REST APIs / GraphQL Vs Blockchain APIs (Infura, Alchemy, Moralis, QuickNode)
APIs connect frontends with backends in web apps. Blockchain APIs connect DApps with blockchain data and smart contract functions, often without running a local node.
DevOps Tools (CI/CD, Docker, GitHub Actions) Vs Blockchain DevOps / Deployment Tools (Ganache, IPFS, Chainlink Keepers, Hardhat Deploy)
Traditional DevOps tools manage development, testing, and deployment pipelines, whereas Blockchain DevOps/Deployment tools are used to simulate local blockchains (like Ganache), run testnets, automate deployment, and integrate with decentralized file storage (IPFS).
Authentication Systems (OAuth, JWT, Session Tokens) Vs Wallet-Based Authentication (Digital Signatures, Wallet Connect)
In a Blockchain system instead of login systems, users authenticate by signing transactions with their private keys via their wallets. No username/password required.
Load Balancers / CDNs Vs Distributed Consensus + Peer-to-Peer Network
Load balancers manage traffic in web apps. In blockchain, the peer-to-peer network and consensus mechanisms (like Proof of Work / Proof of Stake) ensure distributed load, availability, and fault tolerance.
Application Logs / Monitoring Tools Vs Block Explorers (Etherscan, BSCScan, Solscan)
Instead of app logs, blockchain activity is transparently logged on-chain. Block explorers allow anyone to view transactions, contracts, balances, and events — like public logs for the entire system.
File Storage Systems (S3, Google Drive, Local Storage) Vs Decentralized Storage (IPFS, Arweave, Filecoin)
Blockchain can store file references or hashes on-chain and actual content (documents, images, and large files) on decentralized file systems.
Blockchain is not just a database — it’s an entire computing paradigm similar to how a full-stack application includes servers, backend, frontend, APIs, security layers, and deployment tools. By mentally mapping these components, anyone familiar with traditional tech stacks can start to intuitively understand how blockchain ecosystems operate and evolve.
What actually is a Digital Credential?
A digital credential is an electronic version of a qualification, certification, or achievement that is issued, stored, and verified using digital technologies—often on a blockchain or through a secure credentialing platform.
What It Typically Contains?
A digital credential may include but not limited to Recipient’s Name, Issuing Organization, Credential Title (e.g., Bachelor’s Degree in Computer Science), Issue Date, Expiration Date (if applicable), Unique Identifier (e.g., a hash or DID), Metadata, e.g., course details, learning outcomes, grade or anything particular to the achievement.
Key Characteristics
Tamper-proof: Often cryptographically signed (e.g., using blockchain).
Verifiable: Third parties can confirm authenticity without contacting the issuer.
Portable: Can be shared via a digital wallet, QR code, or secure link.
Owned by the user: Stored in a digital wallet or personal account.
Interoperable: Follows standards like Open Badges or Blockcerts.
Examples in Practice
- A university degree issued via Blockcerts
- A certification badge from Coursera or LinkedIn Learning
- A digital transcript issued by an accredited college
- A micro-credential for completing a specialized skill course
What are Digital Signatures and how are they implemented?
Implementing digital signatures in a blockchain-based property deed system is crucial for ensuring legal authenticity, protecting against fraud, and creating a tamper-proof digital record. Here’s how a secure and practical digital signature mechanism works, step by step:
What is a Digital Signature (In Simple Terms)?
A digital signature ensures:
- Authenticity – the signer is who they say they are
- Integrity – the document wasn’t changed after signing
- Non-repudiation – the signer can’t deny signing it
It’s like an unforgeable digital version of signing a paper deed—but way more secure.
Where You’ll Use Digital Signatures?
- When the property buyer and seller agree on terms
- When title companies or real estate attorneys validate the transfer
- When recording the deed on a blockchain-based ledger
Step-by-Step Digital Signature Mechanism
Key Pair Generation
Each party (buyer, seller, authority) uses a Private key – kept secret, used for signing and a Public key – shared openly, used for verification. These keys can be generated via a secure mobile/web application or a licensed Certificate Authority (CA) such as DigiCert, Entrust, or IdenTrust.
Get Certified (For Legal Trust)
To ensure legal validity in the U.S. use a Digital Signature Certificate (DSC) issued by a trusted CA. Tie certificates to real identities (e.g., SSN, driver’s license). For legal compliance, integrate with U.S. CAs compliant with ESIGN Act and UETA (Uniform Electronic Transactions Act).
Create the Property Deed Payload
When all parties complete the digital form. Note that this is just a simple example:
{
"sellerName": "Jane Smith",
"buyerName": "John Doe",
"propertyAddress": "1234 Elm Street, Austin, TX 78701",
"salePrice": "$650,000",
"timestamp": "2025-07-19T15:30:00Z",
"titleID": "TX-2025-7821-RE"
}
Sign the Payload
Each party signs the JSON (or hash of it) with their private key:
signature = sign(privateKey, hash(payload))
This generates a unique digital signature for that document.
Attach the Signature to the Deed
The digitally signed deed may look like this:
{
"payload": { ... },
"sellerSignature": "base64-encoded-signature",
"buyerSignature": "base64-encoded-signature",
"publicKeys": {
"seller": "...",
"buyer": "..."
}
}
You can either store the full record on-chain (if it’s small) or store only the hash on-chain, with the full file in IPFS or a secure cloud.
Verify Signatures
Anyone (such as a county recorder, title company, or court) can verify the digital signatures using code like:
isValid = verifySignature(publicKey, signature, hash(payload))
Only the true signer’s key will validate.
Implementation Tools
- Key Generation: Web Crypto API, OpenSSL, Ethereum wallets (e.g. MetaMask)
- Signing/Verifying: Node.js crypto, Python ecdsa, Go crypto/ecdsa
- Certificate Authority: DigiCert, Entrust, IdenTrust, GlobalSign (U.S.-based CAs)
- Blockchain Signature Log: Ethereum, Hyperledger Fabric, Tezos
- Mobile Key Storage: iOS Secure Enclave, Android Keystore, Web3 wallets
Legal Binding in the U.S.
To ensure the signatures are legally binding, confirm that 1- You’re using certified CAs recognized under ESIGN and UETA, 2- Users’ identities are verified during the key issuance, The blockchain solution records timestamps and immutable logs.
How Can Blockchain Facilitate Academic Degree Issuance and Verification?
Objective: Create a decentralized system to issue, store, and verify academic degrees using blockchain, eliminating fraudulent claims, simplifying employer verification, and ensuring lifelong accessibility for graduates.
1: Identify the Stakeholders
- Universities & Educational Institutions: Issue degrees as digital credentials.
- Graduates / Students: Receive secure, verifiable digital degrees.
- Employers / Verifiers: Verify authenticity of academic records.
- Accreditation Bodies / Government: Optionally supervise compliance and authenticity.
Step 2: Define the Key Blockchain Components
| Component | Purpose |
| Smart Contracts | Define the issuance rules and access rights |
| Public/Private Key | Used by universities to sign digital degrees |
| Blockchain Ledger | Stores hashes of degree credentials |
| Off-chain Storage | Stores actual degree documents (e.g., IPFS or encrypted cloud) |
| Decentralized Id (DID) | Assigns verifiable identity to institutions and students |
Step 3: Create the Smart Contract Design
Smart contracts are deployed on the blockchain (e.g., Ethereum, Hyperledger Fabric) to:
- Register universities as verified issuers.
- Issue degrees by writing a hash of the credential to the blockchain.
- Link the hash to a DID of the student.
- Allow third-party read-only access (for verification).
Step 4: Degree Issuance Workflow
- Student Graduates.
- The university digitally signs the degree in PDF or JSON format or other. Degree document is stored off-chain (e.g., in IPFS) and hashed using SHA-256
- Hash + metadata (student DID, degree type, timestamp) is written to blockchain.
- Student receives a digital credential (wallet or app-based).
Step 5: Verification Workflow
When an employer or third party wants to verify a degree:
- Student shares a link or QR code pointing to their credential.
- Verifier reads metadata from blockchain. re-hashes the off-chain document and matches it with the on-chain hash.
- If match is successful, the credential is authentic and untampered.
Step 6: Third-Party Integrations
- Digital Wallets for students (e.g., Blockcerts wallet)
- Verification Portals for employers
- University APIs to automate issuance
- Cloud Storage or IPFS nodes for storing full documents
- Blockchain platform: Ethereum (public) or Hyperledger (permissioned)
Step 7: Legal, Compliance & Data Privacy
- Ensure compliance with FERPA (Family Educational Rights and Privacy Act)
- Use permissioned blockchain if sensitive data is involved
- Encrypt off-chain documents and use access-controlled sharing
Benefits of Blockchain-Based Degree Verification
- Tamper-proof and instantly verifiable degrees
- No more fake credentials
- Reduces university verification load
- Global accessibility of academic records
- Lifelong validity and ownership by student
Real-World Examples
- MIT Media Lab + Learning Machine (now Hyland Credentials) built Blockcerts—a real blockchain-based degree issuance solution.
- National Student Clearinghouse (U.S.) is exploring blockchain for secure education records.
- Georgia Tech and University of Bahrain have issued digital diplomas via blockchain.
If an organization runs a blockchain system, say for the purpose of university degree issuance, verification and storage. In which ways an individual can get themselves added in that blockchain network; like being a developer, a custodian of a node, mining etc. ?
Ways an Individual Can Participate in That Blockchain System
As a Developer / Technical Contributor
How: Join the development team that designs, builds, or maintains the smart contracts, user interfaces, APIs, and backend.
Skills needed: Blockchain development (e.g., Solidity, Fabric chaincode), backend dev (Node.js, Python, Go), smart contract auditing, DevOps.
Access route: Be hired by the company (or a tech vendor they use). Contribute if the project is open-source (rare for private systems)
Typical role in design, programming, smart contract logic, integration with university systems.
As a Node Operator / Infrastructure Manager
How: Operate a node (hardware/software) that hosts a copy of the blockchain, validates transactions, and ensures data integrity.
Possible for individuals? Yes — but only with permission from the blockchain’s admin.
Possible Roles: For instance, 1- University IT team, 2- Third-party verifier (e.g., education boards or partner universities), 3- Government regulators
To assume a Notes Operator or Infrastructure Manager position you must be authorized by the company — this is not open to the public like Bitcoin.
As a Verifier / Validator (Non-mining)
How: You verify degrees using interfaces (e.g., a portal or blockchain API).
Public or restricted access: Some blockchains allow read-only public access to data. Others require login/API keys for validation
Remember that you’re using the blockchain but not the stakeholder or part of the infrastructure.
As a Miner?
In private or permissioned systems like this, mining doesn’t exist the way it does in public blockchains.
Consensus is often handled by: 1- Practical Byzantine Fault Tolerance (PBFT), 2- Proof of Authority (PoA), 3- Raft / Kafka-based ordering service (Hyperledger)
No individual mining roles — block creation is coordinated by the system’s internal consensus protocol.
Who Grants Access in This System?
The admin organization (the company/university or a governing board) decides:
- Who joins
- What roles they play (developer, node operator, API user)
- What data is accessible to whom
In many cases, a legal agreement or partnership is required before you’re given access as a participant.
What are Smart Contracts? are they programming logic, if yes then which entity is authorized to program and execute it?
What Are Smart Contracts?
Smart contracts are self-executing agreements with the terms and logic written in code that runs on a blockchain.They automatically enforce and execute rules when certain conditions are met — without the need for intermediaries.
Are Smart Contracts Programming Logic?
Yes, they are pieces of programming logic/code. They contain: Conditions (if/then logic), Functions (what to do when triggered), Permissions (who can interact with it), and Data stored on the blockchain.
They are deployed to, and executed on, a blockchain platform like: Ethereum (most popular, uses Solidity language), Binance Smart Chain, Solana,Cardano, etc.
Who Programs and Executes Smart Contracts?
| Entity | Role in Smart Contracts |
| Developers | Write and test the code (using languages like Solidity, Rust, Vyper) |
| Deployers (individuals, startups, organizations, governments) | Upload the smart contract to a blockchain, paying a fee (e.g, gas cost) |
| Blockchain Network (e.g., Ethereum nodes) | Validates and executes the smart contract logic automatically |
| Auditors/Security experts | Review the contract for bugs or vulnerabilities (very important) |
| Users | Interact with the smart contract via apps or wallets (e.g., sending tokens, signing agreements) |
Who Is Authorized to Program It?
There’s no central authority like a government regulator in most public blockchain platforms. But:
Anyone with technical skill can write and deploy smart contracts.
Organizations or governments may set internal policies and approval workflows before deploying them.
In permissioned/private blockchains, only approved entities can deploy or interact with smart contracts.
Real-World Example (Share / Security Tokenization)
- A company tokenizes its shares as security tokens, where each token represents legal ownership in the company and is governed by a smart contract.
- The smart contract maintains shareholder records, ownership percentages, voting rights, and dividend eligibility, while enforcing compliance rules such as KYC and transfer restrictions.
- After the company’s quarterly, bi-annually or annual financial review, the board approves a dividend distribution based on declared profits.
- Once approved, the smart contract automatically calculates each shareholder’s entitlement and distributes dividends to token holders’ wallets in stable coins or tokenized fiat.
- All ownership changes and dividend transactions are recorded immutably on the blockchain, ensuring full transparency and verifiability.
Summary
| Concept | Description |
| Smart Contract | Code stored on a blockchain that automatically executes actions |
| Language | Solidity, Rust, Vyper, etc. |
| Authorized Entity | public blockchain = anyone private = restricted |
| Execution | By blockchain nodes — decentralized and automatic |
Example: A very simple Smart Contract to Store and Retrieve a Message
// SPDX-License-Identifier: MIT
pragma solidity ^0.8.0;
contract MessageContract {
string private message; // variable to store the message
// Function to set a message
function setMessage(string calldata _message) public {
message = _message;
}
// Function to get the message
function getMessage() public view returns (string memory) {
return message;
}
}
How This Smart Contract Works:
| Function | Purpose |
| setMessage() | Allows any user to store a message on the blockchain |
| getMessage() | Allows any user to retrieve the stored message |
| message | A private variable, but can still be accessed via the getMessage() function |
| pragma solidity ^0.8.0; | Tells the compiler which version of Solidity to use |
What Happens When Deployed?
- A user deploys this contract to Ethereum using a wallet like MetaMask and a development tool like Remix or Hardhat.
- The contract is stored on the blockchain.
- Anyone can now interact with it using a web interface or directly via blockchain tools:
- Call setMessage(“Hello Blockchain!”)
- Then call getMessage() → returns “Hello Blockchain!”
What is a Digital Wallet in the context of Blockchain?
A digital wallet, both in the context of blockchain and otherwise, serves as a tool to store and manage digital values or credentials.
Digital Wallet in the Blockchain Context
A blockchain-based digital wallet (also called a crypto wallet) is a software or hardware application that allows users to 1- Store, manage, and transfer cryptocurrencies (e.g., Bitcoin, Ethereum), 2- Sign transactions cryptographically, 3- Interact with decentralized applications (dApps) and smart contracts.
Contrary to common belief, it doesn’t store actual coins. Instead, it stores 1- Private keys: Needed to authorize and sign transactions, 2- Public keys and wallet addresses: Used to receive funds.
Types of Blockchain Wallets
- Hot Wallets (connected to the internet)
- Mobile apps (e.g., Trust Wallet, MetaMask)
- Desktop apps (e.g., Electrum)
- Web wallets (e.g., Blockchain.com)
- Cold Wallets (offline for higher security)
- Hardware wallets (e.g., Ledger, Trezor)
- Paper wallets (physical QR code with keys)
Blockchain wallets are mainly used for sending and receiving crypto assets, accessing DeFi platforms, and participating in token sales, NFTs, and staking.
Key Differences
| Feature | Blockchain Wallet | Traditional Digital Wallet |
| Stores | Private keys for crypto assets | Bank cards, tickets, loyalty points |
| Linked to | Blockchain address | Bank account / credit card |
| Custody | Often user-controlled (non-custodial) | Custodial by bank or service provider |
| Internet dependency | Hot wallets need it, cold wallets don’t | Usually needs internet/NFC |
| Use case | Crypto, NFTs, DeFi, smart contracts | Contactless payments, ID storage |
| Regulations | Often unregulated or semi-regulated | Fully regulated financial service |
A digital wallet is essentially a digital container for value or credentials. On the blockchain, it empowers you to interact with decentralized finance and own crypto.
What is DeFi and how does it extend the power of Blockchain?
Decentralized Finance, commonly known as DeFi, represents a transformative layer built on top of blockchain technology that aims to recreate traditional financial systems without relying on centralized financial institutions like banks or brokers. Instead of intermediaries, DeFi uses smart contracts—self-executing programs stored on the blockchain—to facilitate financial activities such as lending, borrowing, trading, and earning interest. These systems operate on decentralized networks, allowing users to interact directly with protocols through digital wallets, thereby reducing dependency on traditional financial gatekeepers.
What makes DeFi particularly compelling is its ability to democratize access to financial services. Anyone with an internet connection can participate, regardless of geographic or economic barriers, which is a stark contrast to conventional banking systems. At the same time, this openness introduces new dynamics where users are fully responsible for their assets and decisions. While DeFi showcases the true potential of blockchain in reshaping finance, it also highlights the importance of understanding risks, as the absence of intermediaries means there is no fallback in case of errors or vulnerabilities.
What are NFTs and how do they redefine digital ownership?
Non-Fungible Tokens, or NFTs, are a unique class of digital assets that exist on a blockchain and represent ownership of a specific item, whether digital or physical. Unlike cryptocurrencies such as Bitcoin, which are interchangeable and identical in value, NFTs are distinct and cannot be exchanged on a one-to-one basis. Each NFT carries unique metadata and an identifier that verifies its authenticity and ownership, making it ideal for representing digital art, collectibles, virtual real estate, and even identity-related assets.
The real innovation behind NFTs lies in how they redefine ownership in the digital world. Traditionally, digital content could be copied endlessly without any concept of scarcity or provenance. NFTs introduce a verifiable layer of ownership, enabling creators to monetize their work directly while allowing buyers to own something provably unique. However, it is important to understand that owning an NFT does not always grant full legal rights to the underlying asset, and the value of these tokens is often driven by market perception and demand rather than intrinsic utility.
What are the key limitations and challenges of Blockchain technology?
Despite its revolutionary potential, blockchain technology is not without its limitations, and understanding these challenges is essential for a balanced perspective. One of the most significant issues is scalability, as many blockchain networks struggle to handle a large volume of transactions efficiently, leading to slower processing times and higher costs. Additionally, the decentralized nature of blockchain, while beneficial for security and transparency, introduces complexity that can make systems difficult to design, maintain, and use for the average person.
Another major concern lies in regulatory uncertainty and security risks. Since blockchain operates across borders and often without central authority, governments and institutions are still trying to establish appropriate legal frameworks. This lack of clarity can create hesitation among uses, specifically the large businesses. At the same time, reported vulnerabilities in smart contracts and decentralized applications have led to hacks and financial losses, highlighting that the technology, while robust in theory, is still evolving in practice. Furthermore, issues such as energy consumption in certain consensus mechanisms and market volatility add additional layers of concern that must be addressed for widespread adoption.
What are the key functions that are commonly being explored or implemented using Blockchain technology?
Following are the major key functions that are or can be explored using Blockchain technology:
Government & Legal
Property title registration and transfer
Blockchain enables secure, tamper-proof recording of property titles, reducing fraud and simplifying land ownership verification and transfer.
Vehicle sale and ownership tracking
Ownership history and sale transactions of vehicles can be logged immutably, minimizing disputes and paperwork.
Digital identity and authentication
Individuals can manage secure, verifiable digital identities, reducing identity theft and streamlining access to services.
Voting systems (secure e-voting)
Blockchain can power transparent, tamper-resistant digital voting systems that ensure voter anonymity and trust in election results.
Public records and Notary services
Government records and notarized documents can be timestamped and stored immutably on blockchain, increasing public trust and accessibility.
Finance & Banking
Cross-border payments
Blockchain reduces the cost and time for international money transfers by removing intermediaries and offering real-time settlement.
Smart contracts for loans and insurance
Automated contracts trigger actions like disbursements or claims upon meeting predefined conditions, improving efficiency and transparency.
Fraud detection and audit trails
Every transaction on blockchain is traceable and permanent, enabling better auditing and fraud prevention.
Tokenized Securities and Asset Trading
Physical assets and financial instruments can be represented as tokens, allowing fractional ownership and faster trading.
Decentralized finance (DeFi) platforms
DeFi allows users to borrow, lend, or trade assets directly via blockchain-based protocols without traditional banks.
Supply Chain & Logistics
Product provenance and tracking
Blockchain helps trace a product’s journey from origin to consumer, ensuring authenticity and reducing counterfeiting.
Anti-counterfeit verification
Secure blockchain tags or records verify product legitimacy, especially for luxury goods, electronics, or pharmaceuticals.
Cold-chain monitoring for pharmaceuticals and food
Blockchain-integrated IoT devices record temperature data, ensuring sensitive goods are transported under required conditions.
Automated customs and compliance
Smart contracts and transparent tracking streamline cross-border documentation and compliance checks.
Healthcare
Electronic health record (EHR) sharing
Blockchain allows patients and providers to securely share health records while maintaining data integrity and privacy.
Patient consent and data privacy
Patients can control who accesses their health data, with consent logs permanently stored on the blockchain.
Drug traceability and recall management
Blockchain enables end-to-end tracking of medicines, helping detect counterfeit drugs and streamline recalls when needed.
Energy & Utilities
Peer to peer energy trading
Homeowners with solar panels can sell excess power directly to neighbors using blockchain-based energy platforms.
Carbon credit tracking
Blockchain ensures transparent issuance, trading, and retirement of carbon credits, reducing double counting and fraud.
Grid and usage optimization
Energy consumption data recorded on blockchain can help utilities optimize grid performance and demand forecasting
Education & Credentials
Academic degree verification
Institutions can issue tamper-proof digital diplomas, and employers can instantly verify their authenticity on blockchain.
Skill and certification tracking
Blockchain enables a lifelong, verifiable record of skills and professional achievements accessible across institutions.
Intellectual Property & Media
Digital rights management (DRM)
Blockchain ensures content creators retain control over distribution rights and can enforce usage rules via smart contracts.
Royalty distribution via smart contracts
Artists and rights holders can receive automatic, transparent royalty payments whenever their content is used or sold.
Authenticity verification for digital art (NFTs)
Non-Fungible Tokens (NFTs) prove originality and ownership of digital art, helping prevent unauthorized copies and fakes.
Common Questions About Blockchain Technology
Why is Blockchain considered secure?
Blockchain is considered secure primarily because of its decentralized and cryptographic nature. Instead of relying on a single central authority, blockchain distributes data across multiple nodes, making it extremely difficult for any single entity to manipulate the system. Each transaction is linked to the previous one using cryptographic hashes, forming a chain that is inherently resistant to tampering.
However, security in blockchain is not absolute—it is probabilistic. The more distributed and widely adopted a blockchain network is, the more secure it becomes. Large networks like Bitcoin are practically immutable due to the immense computational power required to alter past records. This layered design—decentralization, consensus mechanisms, and cryptography—collectively forms the backbone of blockchain security.
Can Blockchain be hacked or compromised?
The idea that blockchain is completely “unhackable” is a common misconception. While the core blockchain structure is highly secure, vulnerabilities can exist in the surrounding ecosystem, such as poorly written smart contracts, weak wallet security, or centralized exchanges.
In rare cases, attacks like the 51% attack can theoretically compromise a blockchain network, where a single entity gains control over the majority of computational power. However, executing such an attack on large networks is extremely costly and impractical. In reality, most blockchain-related breaches occur outside the blockchain itself, reinforcing the importance of secure implementation rather than relying solely on the technology.
Why is Blockchain often considered slow?
One of the trade-offs of blockchain technology is performance. Unlike traditional databases that process transactions centrally and rapidly, blockchain requires consensus among distributed nodes before confirming a transaction. This validation process, while enhancing security and trust, introduces latency.
Additionally, block size limitations and network congestion can further slow down transaction throughput. While newer blockchain technologies are addressing scalability through innovations like sharding and layer-2 solutions, the balance between speed, security, and decentralization remains a fundamental design challenge.
What are the real-world use cases of Blockchain beyond Cryptocurrency?
While blockchain is often associated with cryptocurrencies, its applications extend far beyond digital currencies. Industries such as supply chain management, healthcare, finance, and digital identity are actively exploring blockchain to enhance transparency and reduce fraud.
For example, blockchain can be used to track goods across supply chains, ensuring authenticity and reducing counterfeiting. In healthcare, it can securely manage patient records while preserving privacy. These real-world implementations highlight blockchain’s potential as a foundational technology for trust in digital ecosystems.
Blockchain is a huge sphere that has an immense potential to cover loads of significant daily transactions under financial, legal, educational, healthcare and numerous other domains. Having a distributed nature on the part of execution, management and storage it liberates users from the oligarchy of limited organizations or groups, fostering transparency and trust. This provides an alluring experience to the users while making the entire process of creating and managing blocks that represent their precious assets and credentials. With the passage of time the inclusion of more domains and more reliance of the common people on it, the blockchain system is poised to become part and parcel of daily digital life of the users at large. Ultimately, blockchain’s trajectory suggests not just a technological innovation, but a foundational pillar in re-shaping the future of secure and inclusive digital ecosystems.